Cybersecurity for Industrial IoT: How to Protect Your Factory Floor Without Slowing Down IIoT Adoption
In December 2023, a water treatment facility in Aliquippa, Pennsylvania was hacked through an internet-exposed Unitronics PLC. The attackers — linked to an Iranian state group — gained access because the PLC was connected directly to the internet with default credentials. The incident didn't cause physical harm, but it demonstrated a truth that manufacturing CISOs have been warning about for years: the convergence of IT and OT networks creates attack surfaces that most industrial organizations aren't prepared to defend.
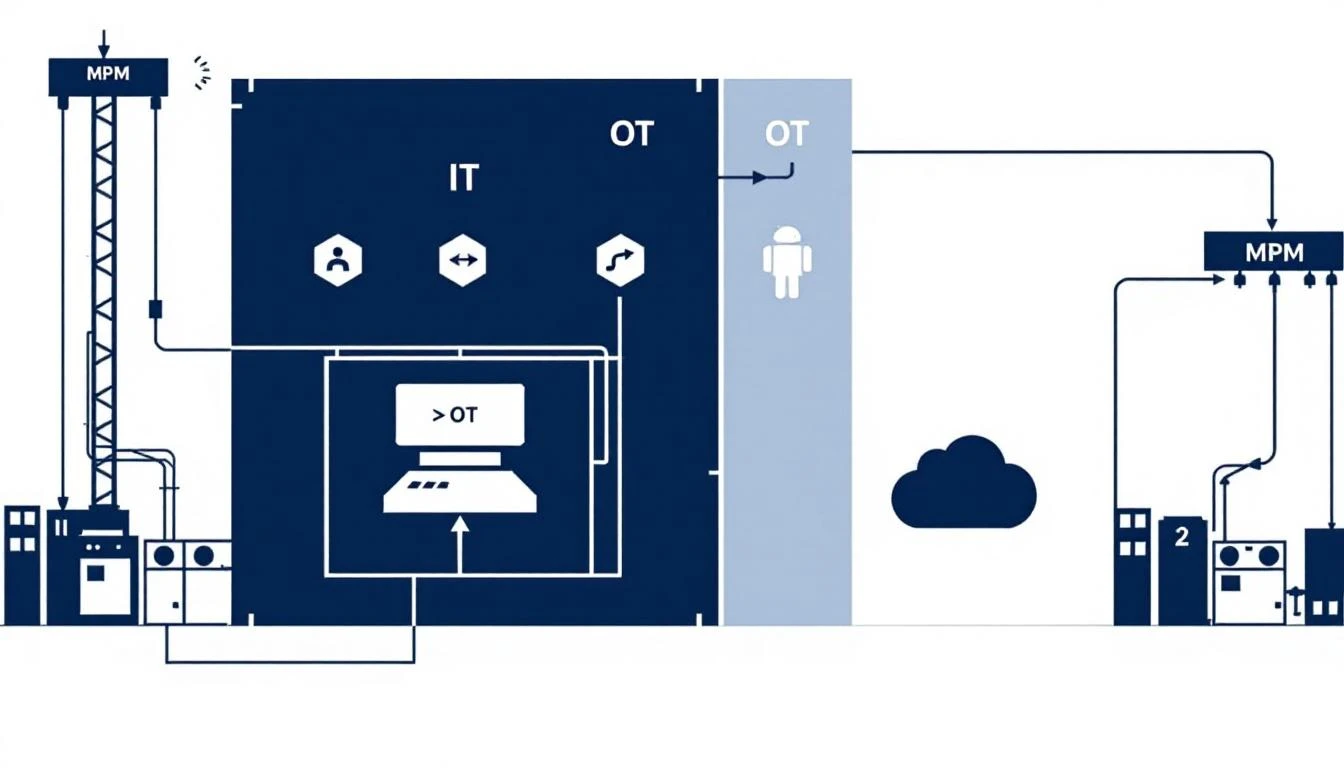
The Purdue Model — the traditional air-gapped architecture that kept operational technology physically separated from information technology — is dissolving. IIoT platforms, cloud analytics, remote monitoring, and digital twins all require connectivity between the factory floor and the outside world. This connectivity delivers enormous value (real-time visibility, predictive maintenance, AI-driven optimization), but it also creates pathways that attackers can exploit.
According to Dragos' 2024 OT Cybersecurity Year in Review, ransomware attacks against industrial organizations increased 50% year-over-year. CISA reported 1,200+ vulnerabilities in industrial control systems in 2024 — up from 800 in 2022. The threat isn't theoretical.
But here's the critical nuance that gets lost in cybersecurity conversations: the alternative to connected IIoT isn't "safe." Plants running disconnected, unmonitored equipment aren't secure — they're blind. They can't detect anomalous equipment behavior, they can't identify compromised controllers, and they can't distinguish between a mechanical failure and a cyber attack manipulating process parameters.
The right approach isn't to avoid IIoT. It's to implement IIoT with a security architecture that protects your operational technology while enabling the visibility and analytics that make your plant safer and more productive.

Understanding the IIoT Attack Surface
Before discussing protection strategies, you need to understand what you're protecting against. IIoT expands the attack surface in four specific ways:
1. Edge Device Exposure
Every IIoT edge device (gateway, sensor, controller) is a potential entry point. If an attacker compromises an edge device, they potentially gain access to the industrial network it's connected to.
Risk factors:
- Edge devices running outdated firmware with known vulnerabilities
- Default credentials that were never changed
- Management interfaces exposed to the internet
- Lack of device authentication (the platform doesn't verify the device's identity)
2. Data in Transit
Data flowing from edge devices to cloud platforms traverses networks that may be interceptable. Process data (temperatures, pressures, production rates) can reveal proprietary manufacturing processes. Control data (setpoints, configurations) can be manipulated in transit.
Risk factors:
- Unencrypted communication protocols (many legacy industrial protocols transmit in plaintext)
- Shared network segments where IIoT traffic mixes with general IT traffic
- Public internet traversal without VPN or TLS encryption
3. Cloud Platform Vulnerabilities
The IIoT platform itself — the cloud dashboard, API, user management system — is a traditional IT attack surface. If compromised, an attacker could view sensitive operational data, manipulate alert thresholds (hiding real problems), or potentially send commands to edge devices.
Risk factors:
- Weak authentication (no MFA, shared accounts)
- Excessive API permissions
- Third-party integrations that expand the attack surface
- Vendor security posture (how well does your IIoT vendor protect their own infrastructure?)
4. OT Network Lateral Movement
The most dangerous scenario: an attacker compromises an IIoT component and uses it to pivot into the operational technology network — reaching PLCs, HMIs, safety systems, and other control equipment.
Risk factors:
- IIoT devices on the same network segment as control systems
- No network segmentation between IIoT data collection and control system networks
- IIoT devices with unnecessary access to control system protocols
The Secure IIoT Architecture: Five Layers of Protection
Layer 1: Network Architecture — Cellular Isolation
The single most effective security measure for IIoT is eliminating the connection between IIoT data collection and your plant's IT/OT network.
Traditional IIoT architectures connect edge devices to the plant Ethernet network, which connects to the corporate network, which connects to the internet, which connects to the cloud platform. Every hop in this chain is a potential compromise point, and lateral movement from any hop can reach the control system network.
Cellular IIoT eliminates this entire attack surface. When the edge device communicates directly with the cloud via cellular connection, there is no pathway from the IIoT system to the plant network. An attacker who compromises the cloud platform cannot reach the control system because there's no network path to traverse.
This is MachineCDN's core security architecture. Edge devices connect via cellular, completely bypassing the plant network. Zero IT involvement means zero IT attack surface. The edge device reads data from PLCs via a dedicated Ethernet connection, but the data flows out via cellular — creating a one-way data path that doesn't create inbound access to the control network.
Why this matters more than any firewall: Firewalls are permeable by design — they're meant to allow authorized traffic. A cellular architecture isn't permeable at all from the plant network's perspective. There's nothing to misconfigure, no ports to accidentally leave open, no VPN credential that can be stolen.
Layer 2: Device Security — Hardening the Edge
Even with cellular isolation, edge devices themselves need to be secure:
Secure boot: The device should verify firmware integrity on every startup, preventing the execution of tampered firmware. Devices without secure boot can be permanently compromised through firmware modification.
Encrypted storage: Configuration data, credentials, and buffered operational data should be encrypted at rest on the edge device. If a device is physically stolen, the data should be unreadable.
Automatic updates: Edge devices in production environments need OTA (over-the-air) update capability. Devices that require physical access for updates effectively never get updated — and unpatched devices are the number one entry point in industrial cyber attacks.
Unique device identity: Every edge device should have a unique cryptographic identity (certificate-based authentication, not just username/password). This prevents device spoofing and ensures the platform only accepts data from authenticated devices.
Minimal attack surface: The edge device should run only the software required for its function. No unnecessary services, no SSH server listening on the network, no web-based management interface accessible from the plant network.
Layer 3: Data Protection — Encryption Everywhere
In transit: All communication between edge devices and the cloud platform should use TLS 1.3 (minimum TLS 1.2). This includes MQTT connections, API calls, firmware updates, and configuration changes. Certificate pinning adds an additional layer by ensuring the device only communicates with the legitimate cloud platform, not a man-in-the-middle impersonator.
At rest: Operational data stored in the cloud should be encrypted. Backups should be encrypted. Database fields containing equipment configurations, process parameters, and alert settings should be encrypted.
In processing: This is the emerging frontier. Confidential computing technologies allow data to be processed in encrypted enclaves, protecting it even from the cloud platform operator. While not yet standard in IIoT, it's coming.
Layer 4: Access Control — Zero Trust for Industrial
Multi-factor authentication (MFA): Non-negotiable for any IIoT platform dashboard. SMS-based MFA is the minimum; authenticator app or hardware key is preferred. According to Microsoft, MFA blocks 99.9% of account compromise attacks.
Role-based access control (RBAC): Operators should see machine status and alerts. Maintenance technicians should see historical data and work orders. Maintenance managers should configure thresholds and routing. Plant managers should see cross-facility dashboards. Nobody should have access they don't need.
Audit logging: Every login, configuration change, threshold adjustment, and data export should be logged with timestamp, user identity, and source IP. These logs are essential for incident investigation and compliance (especially for FDA 21 CFR Part 11 and similar regulations).
Session management: Automatic session timeout, concurrent session limits, and forced re-authentication for sensitive actions (changing alert thresholds, modifying device configurations).

Layer 5: Monitoring and Response — Watching the Watchers
Security monitoring for IIoT should cover three domains:
Platform monitoring: Login anomalies, API abuse, configuration changes, unusual data access patterns. If someone logs into the IIoT dashboard at 3 AM from an IP in a country where you don't have employees, that should trigger an investigation.
Edge device monitoring: Device heartbeat monitoring (a device that stops reporting may have been tampered with or taken offline), firmware version tracking, communication pattern anomalies.
Operational anomaly detection: This is where IIoT security and operational excellence converge. An AI system that detects unusual equipment behavior can catch both mechanical failures AND cyber attacks that manipulate process parameters. If a PLC setpoint changes without a corresponding command from an authorized user, that's both an operational safety issue and a potential cyber incident.
Common IIoT Security Mistakes in Manufacturing
Mistake 1: Connecting IIoT Devices to the Plant Network
This is the most common and most dangerous mistake. Connecting IIoT edge devices to the same network as PLCs, HMIs, and safety systems creates a lateral movement pathway. If the IIoT device is compromised, the attacker is one hop from the control system.
Fix: Use cellular connectivity (MachineCDN's approach) or physically separate IIoT networks with industrial firewalls and one-way data diodes.
Mistake 2: Default Credentials
Default usernames and passwords on edge devices, gateways, and platform accounts are the path of least resistance for attackers. The Aliquippa water plant hack succeeded because of default credentials.
Fix: Change all default credentials before deployment. Use unique credentials per device. Implement certificate-based authentication where possible.
Mistake 3: No Firmware Update Process
Edge devices in production environments frequently run firmware that's 2-5 years old with known vulnerabilities. The "it's working, don't touch it" mentality that's appropriate for PLC programs is catastrophic for security.
Fix: Implement OTA firmware updates with staged rollout (update one device, verify operation, then roll out to fleet).
Mistake 4: Treating IIoT Security as an IT Problem
IIoT security spans IT and OT. IT security teams understand network security and access control but don't understand industrial protocols and safety systems. OT teams understand the plant but may not understand modern cyber threats. Neither team alone can secure an IIoT deployment.
Fix: Create a cross-functional security team with representation from IT security, OT/controls engineering, and plant operations. Define clear ownership for each layer of the security architecture.
Mistake 5: Security as a Reason to Not Deploy IIoT
The most dangerous response to IIoT security concerns is to avoid IIoT entirely. Unmonitored equipment is not secure equipment — it's equipment you can't see, can't analyze, and can't protect. A properly secured IIoT deployment actually improves your security posture by giving you visibility into equipment behavior that can detect both mechanical and cyber-physical anomalies.
Compliance and Standards
Several standards provide frameworks for IIoT security in manufacturing:
- IEC 62443: The gold standard for industrial control system security. Defines security levels, zones, and conduits for OT environments.
- NIST Cybersecurity Framework: Provides the Identify, Protect, Detect, Respond, Recover framework applicable to IIoT.
- ISA/IEC 62443-4-1: Specific to product development security — evaluate whether your IIoT vendor's development practices meet this standard.
- FDA 21 CFR Part 11: For pharmaceutical and food manufacturing, covers electronic records and electronic signatures.
- NERC CIP: For energy sector IIoT deployments, covers critical infrastructure protection.
When evaluating IIoT platforms, ask vendors which standards they comply with and request documentation. A vendor that can't articulate their security architecture in terms of these standards may not have a mature security practice.
Security as a Competitive Advantage
Here's the reframe that forward-thinking manufacturers are adopting: IIoT security isn't a cost center or a compliance checkbox. It's a competitive advantage. Manufacturers with secure, monitored equipment have:
- Better uptime (detecting anomalies that could be either mechanical or cyber-related)
- Stronger customer trust (especially in regulated industries)
- Faster insurance and compliance processes (demonstrable security controls)
- Reduced incident response costs (detecting and containing incidents faster)
MachineCDN's cellular-first architecture was designed with security as a core principle, not an afterthought. No plant network exposure. Encrypted data in transit and at rest. Role-based access control. AI-powered anomaly detection that catches both mechanical and cyber-physical anomalies.
Book a demo and we'll walk through the security architecture in detail — because your IIoT platform should make your plant more secure, not less.
