Industrial Network Security for OT Engineers: TLS, Certificates, and Zero-Trust on the Plant Floor [2026]
Industrial security used to mean padlocking the control room and keeping the plant network air-gapped. Those days ended the moment someone plugged a cellular gateway into the PLC cabinet. Now every edge device streaming telemetry to the cloud is an attack surface — and the cryptominer that quietly hijacked your VM last month was the gentle reminder.
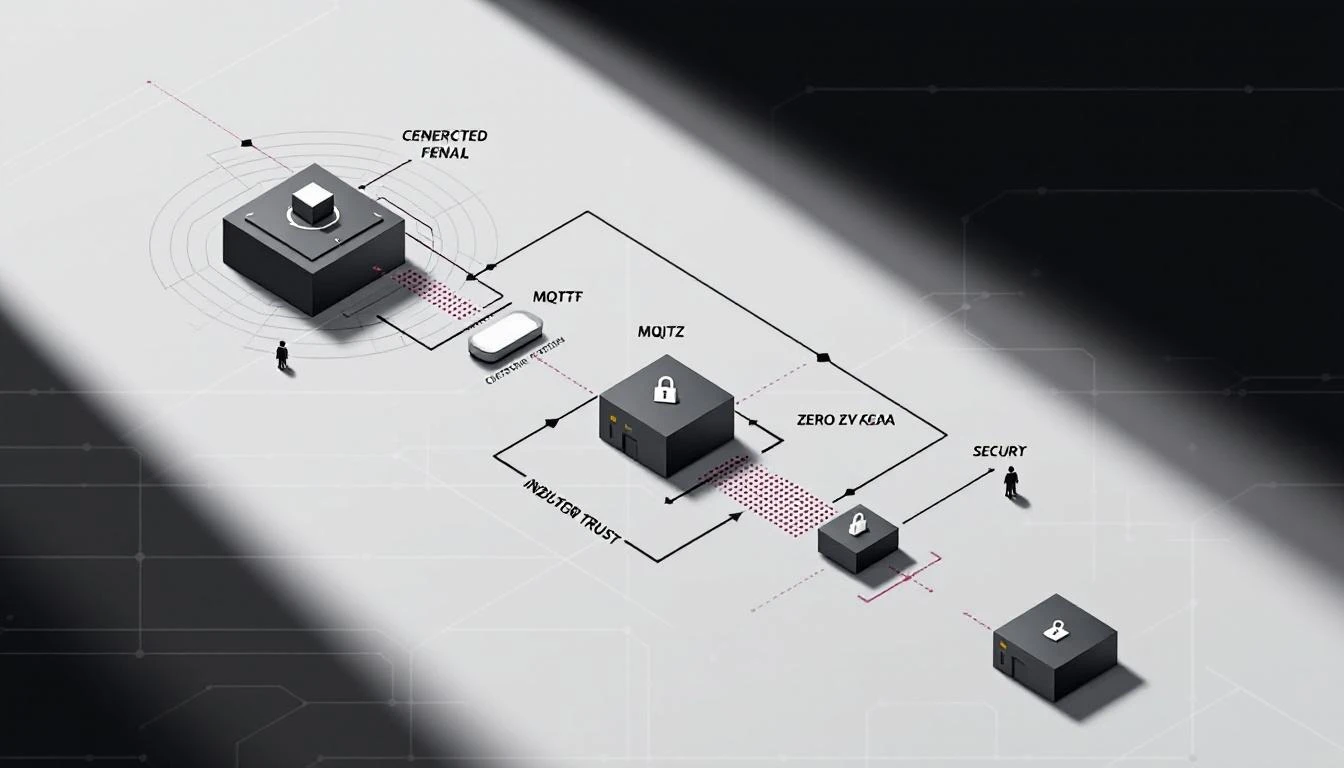
This guide covers the practical security mechanisms you need to protect industrial data in transit — MQTT over TLS, certificate management for OPC-UA and cloud brokers, SAS token lifecycle, network segmentation patterns, and what zero-trust actually means when your "users" are PLC gateways running on ARM processors with 256MB of RAM.